DC Forensic -
Fact-Based Analysis in Sensitive Situations
When digital doubts suddenly become real, it’s not gut feeling that counts, but verifiable analysis. DC Forensic supports private clients in technically proving deception, manipulation, and fake identities – discreetly, objectively, and according to forensic standards. You receive a clear assessment of the evidence and a structured report.
Corporate Forensic Lab
Digital Integrity & Forensic Excellence for Companies
We secure evidence, expose manipulation, and protect your decision-making processes against the threats of the AI era.
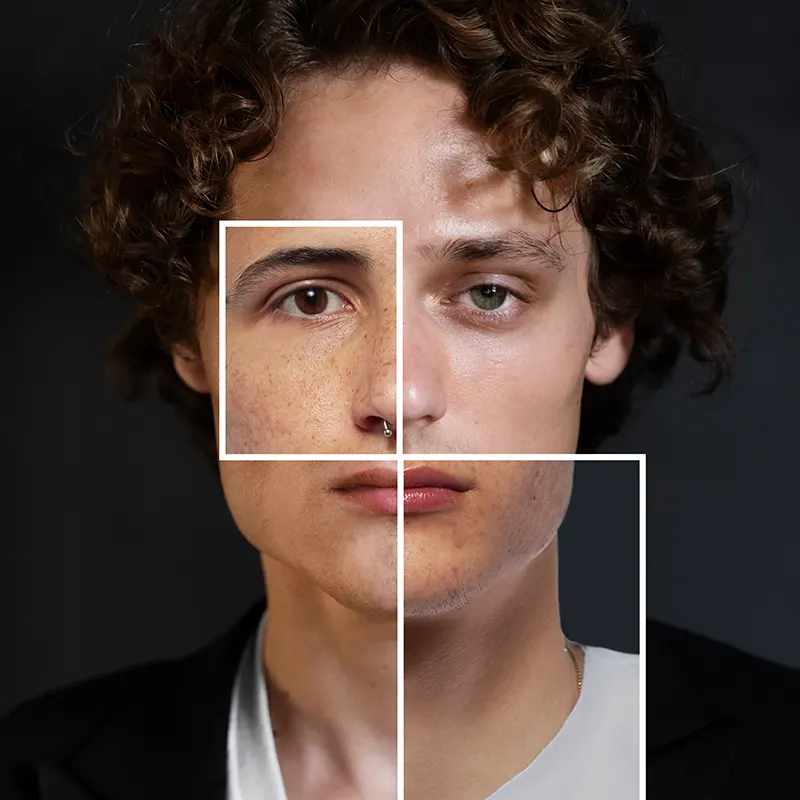
Multimedia Forensics & Authenticity Verification (Core USP)
In a world of deepfakes, we provide certainty.
- Authentication of Images & Video: Testing for AI manipulations, deepfakes, retouching, or frame editing.
- Audio Forensics & Voice Cloning Check: Analysis of voice recordings for speaker identification and proof of technical interference.
- Metadata Reconstruction: Validation of timestamps, GPS data, and hardware IDs for undisputed determination of origin.
- Forensic Image Enhancement: Legally sound processing of blurred footage (CCTV, dashcams) to identify persons or license plates.
Investigation of Economic Crimes & HR Forensics
Clarification of internal and external irregularities.
- Protection Against Data Theft: Proof of unauthorized leakage of know-how or customer lists (especially during personnel changes).
- Detection of Manipulation: Reconstruction of accounting data, deleted emails, or altered log files in cases of suspected fraud.
- HR Forensics & Labor Law: Objective examination of company devices in cases of non-compete violations, bullying, or serious compliance breaches (GDPR-compliant).
- Sabotage Analysis: Identification of traces of targeted system disruptions by insiders or external actors.
Legally Sound Evidence Preservation & Expert Reports
Quality that holds up in court.
- Admissible Documentation: Preparation of expert reports for labor, civil, and criminal proceedings.
- Forensic Imaging: Bit-by-bit backup of data carriers without altering the original (integrity protection).
- Chain of Custody: Seamless documentation of the chain of evidence from initial access to final analysis.
- Insurance Forensics: Independent fact-checking for submission to cyber or liability insurance providers.
Prevention, Awareness & AI Security
Staying one step ahead of the attackers.
- CEO Fraud & Social Engineering Training: Sensitizing executives against fraud schemes (e.g., manipulated via voice cloning).
- AI Pentesting: Stress testing your security systems and identification processes against AI-supported attack scenarios.
- Awareness Training: Staff training for recognizing disinformation, deepfakes, and sophisticated phishing campaigns.
- Prevention Consulting: Establishing verification workflows to protect against authorized misdirected transfers caused by media deception.

Discretion. Precision. Legal Certainty.
Contact
Note: This form is intended only for initial contact. Please do not send any sensitive files or biometric data through this channel. For secure communication, we use our verified, high-security messaging apps in the next step.
AI Pentesting
Technical Validation for the EU AI Act
Deadline August 1, 2026: Are your systems ready?
With the full application of the EU AI Act on August 1, 2026, the requirements for the technical security of AI systems will become a legal obligation. Especially for high-risk applications, the regulation mandates an appropriate level of accuracy, robustness, and cybersecurity under Article 15.
DC Forensic offers independent, purely technical auditing of your AI infrastructure. We act as a specialized testing authority that puts your systems through their paces, enabling you to create the necessary technical documentation on a solid factual basis.
Our main focus areas within the regulation:
- Robustness Testing (Art. 15 Para. 3): We simulate errors, disruptions, and unforeseen environmental conditions to validate the resilience of your model.
- Attack Simulation (Cybersecurity): Targeted checking for AI-specific vulnerabilities such as:
- Adversarial Attacks: Attempts to deceive the model through manipulated inputs.
- Data & Model Poisoning: Analysis of the integrity of training data and components.
- Prompt Injection: Testing susceptibility in Large Language Models (LLMs).
- Detection of Output Manipulation: We test how vulnerable your system is to interventions that could falsify the result.
Forensic facts instead of vague consulting
We see ourselves as technical experts. Our goal is not to redesign your processes, but to uncover your open flanks objectively and with forensic precision.
- Neutral Testing: We evaluate the current state of your technology – independent of software manufacturers or consulting firms.
- Audit Report as an Asset: You receive a detailed evaluation of identified vulnerabilities, serving as technical evidence for your risk analysis and compliance documentation.
- Expert Panel: For highly complex systems, we involve specialists from our international network to cover even the most modern attack vectors.
Technical Deep Dive
Forensic Analysis Procedures
To assess the integrity of digital assets beyond doubt, we apply methods based on signal processing, computer-aided statistics, and reverse engineering of AI architectures.
I. Advanced Image & Video Authentication
We do not view image data as pixel matrices, but as the result of a specific Image Acquisition Pipeline.
- Photo Response Non-Uniformity (PRNU) Analysis: Extraction of the sensor-specific noise pattern using Maximum Likelihood Estimation to verify the link between the medium and the physical sensor (Source Camera Identification).
- CFA Interpolation & Demosaicing Detection: Analysis of interpolation artifacts generated during demosaicing. Inconsistencies in the variance of color channel correlations serve as evidence of local inpainting or splicing.
- JPEG Ghost & Double Compression Detection: Analysis of quantization tables in the frequency domain (DCT coefficients) to localize multiple re-compression cycles and their spatial discontinuities.
II. Neural Network & Generative AI Diagnostics
When identifying deepfakes, we utilize the inherent limitations of current diffusion models and GANs.
- GAN Fingerprinting: Identification of specific up-sampling artifacts (checkerboard effects) caused by transposed convolutions (Conv2DTranspose).
- Latent Space Inconsistency: Checking biometric consistency across time series. We analyze the phenomenon of identity bleeding and inconsistencies in the geometry of corneal reflection vectors.
- Adversarial Robustness Testing: Use of toolkits to check whether the material has been protected or manipulated by adversarial perturbations (targeted noise) to deceive detection algorithms.
III. Audio Engineering & Forensic Acoustics
Forensic audio analysis at DC Forensic is based on physical and biometric parameters.
- Electric Network Frequency (ENF) Matching: Extraction of the 50Hz/60Hz hum signal from the recording and cross-referencing with historical grid frequency databases for temporal authentication.
- Formant & Laryngeal Analysis: Examination of the resonance frequencies of the vocal tract. We use Cepstral analysis to distinguish the physical limitations of human speech from synthetically generated waveforms (vocoders).
- Lossy Compression Artifact Analysis: Examination of the bitstream structure (e.g., MP3/AAC) to prove if the audio material was transcoded from another source (container forensics).
IV. Data Integrity & Bitstream Forensics
- File System & Metadata Carving: Reconstruction of fragmented data structures and analysis of OOV (Out-of-Vocabulary) data in headers.
- Hash Collisions & Blockchain Verification: Use of cryptographic procedures to ensure non-repudiation throughout the entire Chain of Custody.

DC Forensic Lab
Digital Forensic Knowledge Hub
- Deepfake detection: Analysis of AI-generated media for inconsistencies in pixels, noise patterns, or biometrics.
- ELA (Error Level Analysis): Detection of image manipulation through different compression levels within a file.
- Audio spectrogram: Visual inspection of audio recordings for cuts, edits, or synthetic voice components.
- PRNU (Sensor Noise): Identification of the source camera based on the individual "fingerprint" of the image sensor.
- Frame authentication: Frame-by-frame examination of videos to ensure temporal and content integrity.
- Hash value (SHA-256): A digital checksum that ensures that a file has not been altered after it was backed up.
- Write blocker: Hardware that physically prevents a data carrier from being written to while it is being read.
- Forensic image: A bit-for-bit 1:1 copy of a medium, including deleted data areas.
- Slack space: Hidden storage areas at the end of files where traces of deleted data can often be found.
- Data carving: Search for file signatures in "empty" storage space for recovery without file system information.
- Anti-forensics: Techniques used by perpetrators (shredders, encryption) that we neutralize using specialized tools.
- Timeline analysis: Chronological review of all user activities (when was what copied/deleted?).
- Registry forensics: Reading the Windows registry to document installed hardware, programs, and user history.
- Mobile App Artifacts: In-depth analysis of messaging app databases (WhatsApp/Signal) to reconstruct deleted chats.
- IP Attribution: Mapping digital traces to specific network nodes and physical locations.
- Email Header Analysis: We examine an email’s metadata (headers) to verify the actual sender path, the mail servers involved, and the time of transmission. This allows us to detect spoofing (falsified sender addresses).
- Document Metadata (EXIF/XMP): Every PDF or Word document contains hidden information: Who created it? How long was it worked on? Was the creation date altered afterward? We make this “hidden data” visible.
- OCR Forensics (Text Recognition): Making scanned documents or image files searchable to find specific keywords or sensitive information even within thousands of unsorted image files.
- Heuristic analysis: Search for behavior patterns instead of fixed file signatures. This helps us identify new or unknown manipulation methods.
- Encryption analysis (decryption): We examine the type of encryption used for containers or drives. In many cases, we can use forensic tools and computing power (brute force or dictionary attacks) to access encrypted evidence.
- Cross-drive analysis: Comparing data across multiple devices. We check whether a file was moved from laptop A to USB stick B and ultimately ended up on a private PC.
- Browser forensics: Analysis of histories, cache memories, cookies, and session data. We reconstruct web searches, logins, and even form entries that the user made in the browser.
- Wearable forensics: Analysis of smartwatches or fitness trackers. These devices often store more accurate location and health data (e.g., stress pulse during an incident) than the smartphone itself.
- Geofencing analysis: Verification of whether a device was located in a defined geographical area at a specific time, based on GPS logs and Wi-Fi triangulation.
- Cloud backup extraction: Often, the physical device is destroyed or inaccessible. We extract evidence directly from cloud backups (iCloud, Google Dashboard) to restore the digital state.
Yes. Using audio forensics, we analyze the background frequencies (known as "room noise"). An edit almost always causes a minimal irregularity in the frequency response, which we can prove graphically.
Perpetrators often try to tamper with the system clock to falsify alibis. We compare the local system time with the timestamps of file system events and external server logs (e.g., routers or cloud) to restore the true chronology.
In most cases, yes. Standard formatting only deletes the table of contents, not the data itself. As long as the sectors have not been overwritten multiple times with new data, reconstruction is possible.
Here we examine psychological manipulation. We reconstruct the chain of communication (phishing emails, phone calls) to understand how an employee was tricked into bypassing security measures.
DC Forensic
Case Studies - Strategic Investigation for Decision Makers
CEO Fraud & Multimedia Authentication
Scenario: An international industrial company fell victim to a targeted attack. The finance department received a deceptively real voice message (voice cloning) of the CEO, requesting the release of a high special payment.
Our Role: DC Forensic performed an audio spectrogram analysis and identified the synthetic frequency patterns typical for AI-generated voices.
Result: By identifying it as a deepfake, the payment was stopped. We subsequently implemented awareness training for the executive level and established verification workflows to prevent future social engineering attacks.
Leakage of Know-how (Economic Espionage)
Scenario: After a key account manager moved to a competitor, there were indications of the theft of patent drafts and customer lists.
Our Role: Within the framework of HR forensics, we performed forensic imaging of the company device. Using timeline analysis and evaluating registry forensics, we proved the transfer of data to an external medium immediately before the resignation.
Result: A court-admissible expert report was prepared. Based on this, the company obtained a preliminary injunction and successfully asserted claims for damages under the Trade Secrets Act (GeschGehG).
Evidence Preservation in the Microsoft Cloud
Scenario: Suspicion of internal manipulation of accounting data in a hybrid Microsoft infrastructure.
Our Role: As experts in cloud forensics, we secured the audit logs within the Microsoft environment. We analyzed the identity artifacts and proved that access permissions were unauthorizedly changed to conceal transactions.
Result: By adhering to the Chain of Custody, the evidence withstood scrutiny by external auditors. The company was able to close the compliance gap and document the incident according to ISMS standards.